What is OAuth and How It Works in Azure?
Tech Enthusiast | 19+ Years in IT | Security, Coding, Trends With over 19 years of experience in the ever-evolving world of Information Technology, I’m passionate about staying ahead of the curve. From mastering secure coding practices to exploring the latest trends in AI, cloud computing, and cybersecurity, my mission is to share valuable insights, practical tips, and the latest industry updates. Whether it's about writing cleaner, more efficient code or enhancing security protocols, I aim to empower developers and IT professionals to excel in their careers while keeping pace with the rapidly changing tech landscape.
When building applications in the cloud, secure access control is a top priority. We want apps and services to communicate without constantly sharing usernames and passwords. This is where OAuth (Open Authorization) plays a crucial role.
🔹 What is OAuth?
OAuth is an open standard protocol that provides a way to grant access to applications or services without exposing credentials. Instead of sharing your username and password, OAuth uses tokens to grant limited access.
👉 Think of it as giving someone a visitor badge for a specific room in your office, instead of handing over your master key to the entire building.
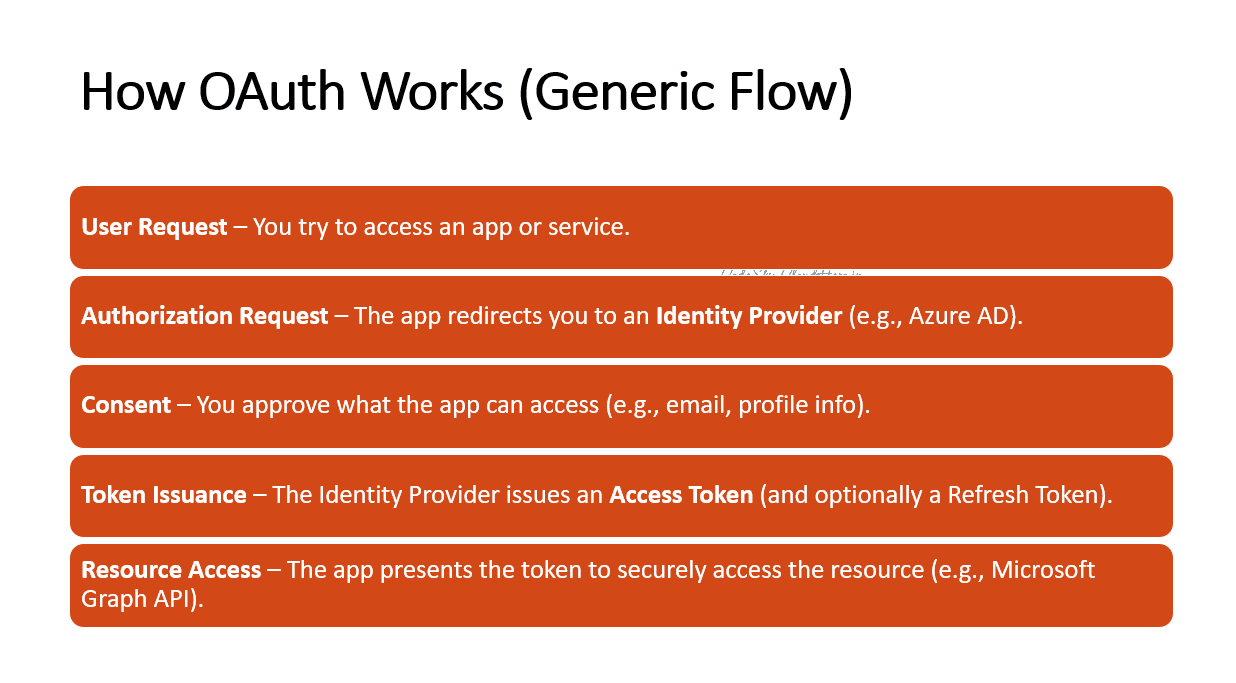
🔹 How OAuth Works (Generic Flow)
User Request – You try to access an app or service.
Authorization Request – The app redirects you to an Identity Provider (e.g., Azure AD).
Consent – You approve what the app can access (e.g., email, profile info).
Token Issuance – The Identity Provider issues an Access Token (and optionally a Refresh Token).
Resource Access – The app presents the token to securely access the resource (e.g., Microsoft Graph API).
🔹 OAuth in Azure
In Azure, OAuth 2.0 is implemented through Microsoft Entra ID (formerly Azure AD). It’s the backbone for authentication and authorization when apps or services interact with Azure resources or Microsoft APIs.
Key Components:
Authorization Server → Azure AD issues tokens.
Resource Owner → The user (or app) granting access.
Client → The application requesting access.
Resource Server → The API or service (e.g., Graph API, Azure Storage) that needs protection.
🔹 OAuth Flow in Azure
App Registration
- The app is registered in Azure AD. It gets a Client ID and optionally a Client Secret.
Authorization Request
- The app redirects the user to Azure AD’s /authorize endpoint.
Consent Grant
- User signs in and grants access. Example: “Allow this app to read your emails.”
Token Exchange
The app exchanges the authorization code with Azure AD’s /token endpoint to receive:
Access Token (short-lived, usually 1 hour)
Refresh Token (longer-lived, used to get new Access Tokens)
Access Resource
- The app uses the Access Token to call APIs such as Microsoft Graph, Azure Key Vault, or custom APIs.
🔹 Example: Using OAuth in Azure
Let’s say you’re building a web app that needs to fetch user data from Microsoft 365.
User signs into the app → redirected to Azure AD.
Azure AD asks for consent: “Allow this app to read your profile and email.”
On approval, Azure AD issues an Access Token.
Your app sends that token to Microsoft Graph API.
Graph API verifies the token → returns the user’s profile and emails securely.
🔹 OAuth Grant Types in Azure
Authorization Code Flow → For web/mobile apps with user sign-in.
Client Credentials Flow → Service-to-service access (no user).
Device Code Flow → For devices without browsers (IoT, CLI).
Implicit Flow → Legacy, for SPAs (being replaced by PKCE).
🔹 Pros of OAuth in Azure
✅ Security – No need to share or store passwords in apps.
✅ Delegated Access – Tokens can be scoped (e.g., read-only vs. full access).
✅ Centralized Identity – Azure AD manages identities and tokens.
✅ Scalability – Works across millions of apps and services.
✅ Compliance – Meets enterprise security and regulatory requirements.
🔹 Cons of OAuth in Azure
⚠️ Complexity – Setting up app registrations, permissions, and flows can be confusing.
⚠️ Token Management – Expiry and refresh handling require extra coding.
⚠️ Over-privilege Risks – If not scoped correctly, apps may request excessive permissions.
⚠️ Learning Curve – Developers need to understand grant types, scopes, and endpoints.
🔹 Final Thoughts
OAuth is not just a buzzword—it’s the foundation of secure cloud authentication and authorization. In Azure, OAuth 2.0 powered by Microsoft Entra ID ensures that apps and services exchange data securely using tokens instead of passwords.
By leveraging OAuth correctly, you can build secure, compliant, and scalable applications that integrate seamlessly with Microsoft cloud services.
✨ Key Takeaway:
OAuth in Azure = secure, token-based delegated access → the right way to protect your apps and data.