Using Network Virtual Appliances (NVAs) in Hub-Spoke Architecture for Secure Traffic Control
Tech Enthusiast | 19+ Years in IT | Security, Coding, Trends With over 19 years of experience in the ever-evolving world of Information Technology, I’m passionate about staying ahead of the curve. From mastering secure coding practices to exploring the latest trends in AI, cloud computing, and cybersecurity, my mission is to share valuable insights, practical tips, and the latest industry updates. Whether it's about writing cleaner, more efficient code or enhancing security protocols, I aim to empower developers and IT professionals to excel in their careers while keeping pace with the rapidly changing tech landscape.
As cloud environments scale, networking becomes more complex. While Azure VNet peering provides seamless connectivity, enterprises often require centralized traffic inspection, logging, and control. This is where Network Virtual Appliances (NVAs) become critical, especially in a Hub-Spoke architecture.
🔹 What is an NVA?
An NVA (Network Virtual Appliance) is a virtualized network function running in Azure, similar to a hardware appliance in on-premises datacenters. It provides advanced security and routing capabilities beyond what Azure-native features (NSGs, UDRs, Service Endpoints) can deliver.
Examples of NVAs:
🔥 Firewalls → Palo Alto, Fortinet, Cisco ASA, Check Point, Sophos
⚡ Load Balancers → F5, Citrix ADC
🌐 Proxies → Web/application proxies for filtering
🔄 Routers → Custom routing and traffic segmentation
🔹 Why Use NVAs in Hub-Spoke Architecture?
Hub-Spoke architecture is a common Azure design pattern:
Hub VNet → Shared services, gateways, security controls
Spoke VNets → Workloads (apps, databases, microservices)
By placing an NVA in the Hub, all inter-spoke and hybrid traffic can be centralized and inspected before reaching its destination.
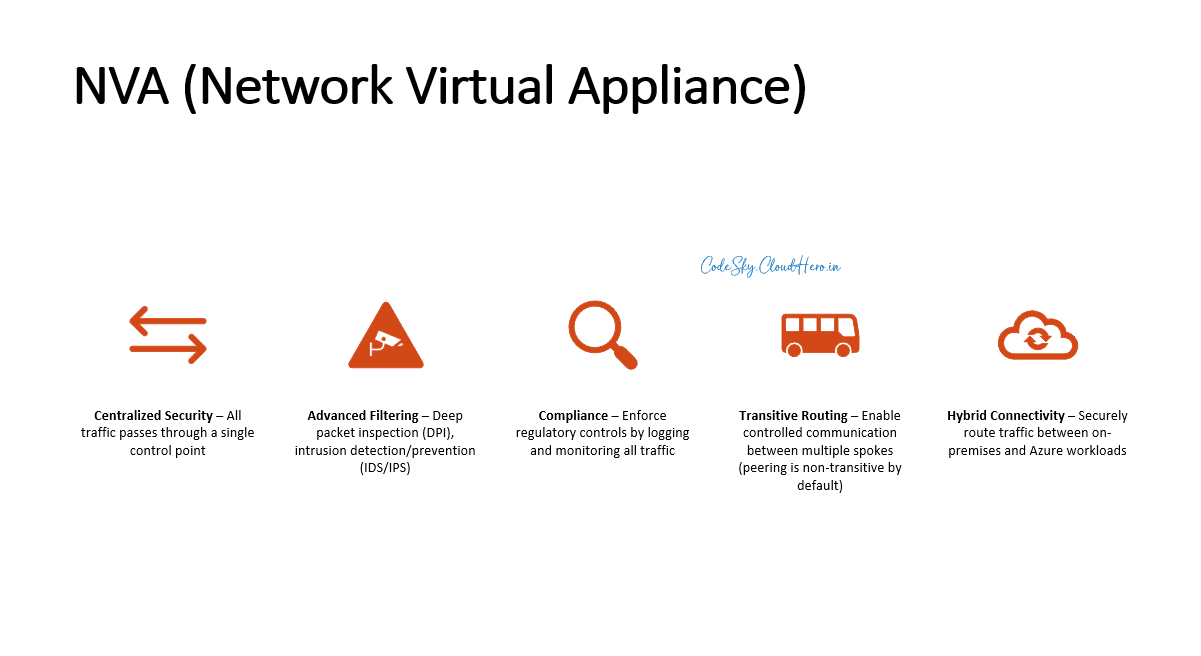
✅ Key Benefits:
Centralized Security – All traffic passes through a single control point
Advanced Filtering – Deep packet inspection (DPI), intrusion detection/prevention (IDS/IPS)
Compliance – Enforce regulatory controls by logging and monitoring all traffic
Transitive Routing – Enable controlled communication between multiple spokes (peering is non-transitive by default)
Hybrid Connectivity – Securely route traffic between on-premises and Azure workloads
🔹 How NVAs Work in Hub-Spoke
Traffic Flow Example
VNet Spoke A (Web App) wants to talk to VNet Spoke B (Database).
Instead of direct peering, traffic is routed:
Spoke A → Hub NVA (firewall) → Spoke BThe NVA inspects, filters, and allows/denies based on rules.
🔹 Step-by-Step Implementation
Step 1: Deploy Hub-Spoke VNets
Hub VNet: contains NVA (Firewall/Router/Proxy)
Spoke VNets: contain workloads (App, DB, Storage, etc.)
Non-overlapping CIDR ranges (e.g., Hub 10.0.0.0/16, Spoke1 10.1.0.0/16, Spoke2 10.2.0.0/16)
Step 2: Deploy the NVA in Hub VNet
Create a VM from the Marketplace (e.g., Palo Alto, Fortinet, Cisco ASA, or Azure Firewall)
Place it in a dedicated subnet (e.g.,
AzureFirewallSubnetorNVA-Subnet)
Step 3: Configure UDRs (User Defined Routes)
Create a Route Table
Add a route for Spoke-to-Spoke traffic → Next hop: NVA private IP
Associate this Route Table with each spoke subnet
Step 4: Configure NSGs
Allow only required traffic (e.g., Web App ↔ SQL DB)
Block unnecessary ports (RDP, SSH, ICMP, etc.)
Apply least-privilege principle
Step 5: Configure the NVA
Define rules (e.g., allow port 1433 SQL traffic, block everything else)
Enable logging for compliance and monitoring
Step 6: Test Traffic Flow
From Spoke A (Web App), test connectivity to Spoke B (DB)
Ensure all traffic flows via NVA in Hub, not directly
🔹 Example Architecture Diagram
On-Premises
|
[ VPN / ER ]
|
[ Hub VNet ]
/ | \
[Spoke A] [NVA] [Spoke B]
| |
Web App SQL DB
- All traffic between Spokes or On-premises passes through the NVA in Hub
🔹 Best Practices
High Availability (HA): Deploy NVAs in an Availability Set or Availability Zones
Scale Out: Use Load Balancers for multiple NVA instances
Central Logging: Integrate with Azure Monitor / Log Analytics
Use Azure Firewall where possible: For a managed, scalable option instead of 3rd-party NVAs
Plan CIDR Ranges Carefully: Prevent overlapping IPs to simplify routing
Monitor Performance: NVAs can become bottlenecks; size them appropriately
🔹 Final Thoughts
NVAs provide enterprise-grade security and control in Azure networking.
When combined with Hub-Spoke architecture, they enable:
Secure spoke-to-spoke communication
Centralized inspection and logging
Compliance with strict regulatory environments
While Azure-native tools like NSGs and Private Endpoints provide foundational security, NVAs bring advanced capabilities like deep inspection, transitive routing, and hybrid connectivity management.
If you’re designing secure, large-scale cloud networks, NVAs in a Hub-Spoke model are a proven solution.
💬 Discussion Prompt:
Do you prefer using 3rd-party NVAs (Palo Alto, Fortinet, Cisco) or Azure Firewall for centralized traffic inspection in your Hub-Spoke setups?
#Azure #CloudSecurity #HubSpoke #NVA #AzureFirewall #CloudArchitecture #Networking