Azure Private Endpoint: Secure Your PaaS Services with Private Connectivity
Tech Enthusiast | 19+ Years in IT | Security, Coding, Trends With over 19 years of experience in the ever-evolving world of Information Technology, I’m passionate about staying ahead of the curve. From mastering secure coding practices to exploring the latest trends in AI, cloud computing, and cybersecurity, my mission is to share valuable insights, practical tips, and the latest industry updates. Whether it's about writing cleaner, more efficient code or enhancing security protocols, I aim to empower developers and IT professionals to excel in their careers while keeping pace with the rapidly changing tech landscape.
In cloud architecture, security and network isolation are paramount. Azure Private Endpoint provides a secure, private connection from your Virtual Network (VNet) to Azure PaaS services, removing reliance on public endpoints.
Whether you are designing highly secure enterprise workloads or regulatory-compliant applications, understanding Private Endpoints is crucial.
🔹 What is a Private Endpoint?
A Private Endpoint is a network interface that connects you privately to Azure services over a private IP address within your VNet.
Key points:
The service appears inside your VNet.
All traffic stays on the Azure backbone, avoiding the public internet.
Works with Azure PaaS services like Storage Accounts, SQL Database, Key Vault, Cosmos DB, and more.
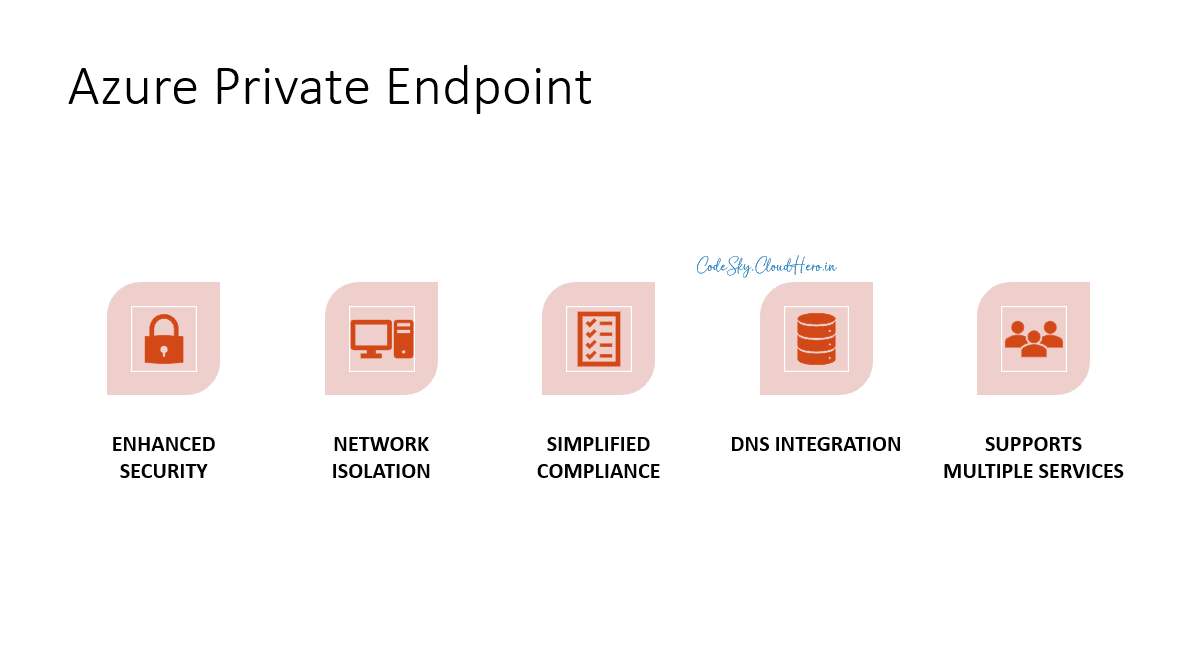
🔹 Benefits of Private Endpoint
Enhanced Security
Eliminates public network exposure.
Supports NSGs to restrict traffic further.
Network Isolation
The service is effectively part of your VNet.
Only VNets/subnets with access can reach the resource.
Simplified Compliance
Reduces risk of public exposure for sensitive workloads.
Meets enterprise security standards and regulatory requirements.
DNS Integration
Private Endpoint integrates with Azure Private DNS.
Resources in the VNet resolve the service to its private IP automatically.
Supports Multiple Services
- Storage Accounts, SQL Database, Key Vault, App Configuration, Cosmos DB, and more.
🔹 Private Endpoint vs Service Endpoint
| Feature | Service Endpoint | Private Endpoint |
| Connectivity | Public IP (Azure backbone) | Private IP in VNet |
| Network Isolation | Subnet-level | Full VNet integration |
| Access Control | NSG + Azure role | NSG + VNet/subnet |
| DNS Resolution | Public DNS | Private DNS resolves private IP |
| Public Exposure | Still accessible publicly | Can block public access completely |
🔹 When to Use Private Endpoint
When you want to secure Azure PaaS resources from public internet exposure.
Regulatory or compliance environments (finance, healthcare, government).
Multi-tier architectures where internal apps need private access to databases or storage.
Hybrid scenarios with on-premises connectivity via VPN or ExpressRoute.
🔹 Step-by-Step Implementation
Step 1: Prerequisites
Existing VNet and subnet
Azure PaaS resource (e.g., SQL Database or Storage Account)
Required permissions: Owner/Contributor on VNet and PaaS resource
Step 2: Create a Private Endpoint
Go to Azure Portal → Private Endpoint → + Create
Select Resource type (Storage Account, SQL, Key Vault, etc.)
Choose the subscription, resource group, and target resource
Step 3: Configure Network
Select Virtual Network and subnet where the Private Endpoint will reside
Enable Private DNS integration (recommended) to allow VNet to resolve the resource’s private IP automatically
Step 4: Approve Connection
- For some PaaS services, the owner of the resource must approve the private endpoint connection
Step 5: Configure DNS
Azure automatically creates a Private DNS Zone linked to your VNet
If using your own DNS:
- Create an A record pointing the service FQDN to the private IP
Step 6: Test Connectivity
Deploy a VM in the same VNet/subnet
Use ping (ICMP) or Test-NetConnection for TCP connectivity
Access the PaaS resource using its private FQDN
Step 7: Restrict Public Access (Optional but Recommended)
Go to the PaaS service → Networking → Disable Public Endpoint access
Only Private Endpoint traffic will be allowed
🔹 Implementation Diagram
[VM/Subnet in VNet] <---> [Private Endpoint] <---> [Azure PaaS Service]
|
+--- NSG, Private DNS
VM in VNet communicates via Private IP
All traffic stays on Azure backbone
Public endpoint can be disabled for maximum security
🔹 Best Practices
Always enable Private DNS integration for seamless name resolution.
Use NSGs to restrict inbound/outbound traffic to the Private Endpoint.
Limit public access to PaaS resources after Private Endpoint creation.
Plan subnets carefully; Private Endpoint consumes IP addresses from the subnet.
Monitor traffic using Azure Monitor and NSG flow logs.
🔹 Final Thoughts
Azure Private Endpoint is key for secure, private, and compliant cloud architectures. By implementing Private Endpoints:
Your workloads are isolated from the public internet
Communication stays on the Azure backbone
DNS and NSG integration provide full network control
When combined with Hub-Spoke or multi-tier architectures, Private Endpoints allow you to build enterprise-grade secure networks on Azure.